Seamless Automation: Endpoint Discovery as the Backbone of Dynamic Infrastructures
In traditional infrastructures, monitoring was a manual process: a new server was rented, an …
In industries like manufacturing, finance, or critical infrastructures, automation is not a “nice-to-have” but a mandatory necessity. Kubernetes is well-established – yet the provisioning of control planes in regulated on-premises environments remains complex.
Virtual machines must be auditable, reproducible, and secure. Standard templates with Ubuntu or CentOS are often challenging to keep up-to-date. At the same time, compliance requires full control over supply chain, secrets, and network access.
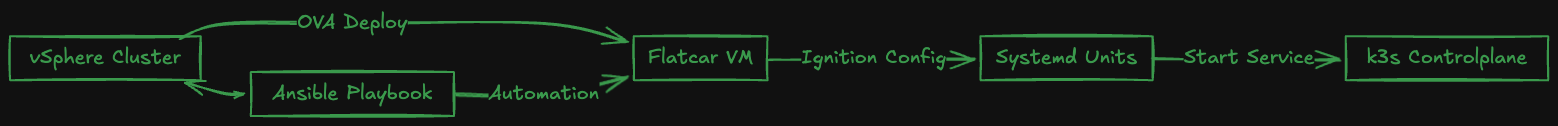
An approach particularly suitable for edge, test, dev, and even prod clusters in sensitive environments: Flatcar Linux + k3s, fully automated provisioning via Ansible on vSphere.
The result: quickly deployed, standardized control planes, without click-ops in vCenter, reproducible from code, and adaptable for air-gapped environments.
community.vmware collection controls VM creation & configuration.guestinfo.In many industries, the drawbacks of Cloud-Init VMs are well-known:
Flatcar + Ignition offers:
Flatcar reads an Ignition JSON file at boot, provided via VMware guestinfo. This describes users, files, units, network – and thus the k3s bootstrapping process.
{
"ignition": { "version": "3.4.0" },
"passwd": {
"users": [
{
"name": "core",
"sshAuthorizedKeys": ["ssh-ed25519 AAAAC..."]
}
]
},
"storage": {
"files": [
{
"path": "/etc/systemd/system/k3s.service",
"mode": 420,
"contents": {
"source": "data:text/plain;charset=utf-8,[Unit]\nDescription=Lightweight Kubernetes\nAfter=network-online.target\n..."
}
}
]
},
"systemd": {
"units": [
{
"name": "k3s.service",
"enabled": true
}
]
}
}Advantage: complete config versioned in the Git repo. Every re-deploy is identical.
With the Ansible collection community.vmware, VMs can be deployed from content library OVAs, Ignition injected, and IP addresses queried.
- name: Provision Flatcar VM and run k3s (single server)
hosts: localhost
collections:
- community.vmware
tasks:
- name: Deploy VM
vmware_content_deploy_ovf_template:
hostname: vcsa.lab.local
username: svc_ansible@vsphere.local
password: "{{ vcenter_password }}"
datacenter: "DC1"
cluster: "Compute"
datastore: "vsanDatastore"
name: "cp1"
content_library: "BaseImages"
template: "flatcar-stable-vmware.ova"
folder: "/DC1/vm/k3s"
networks:
- name: "VM Network"
power_on: true
advanced_settings:
- key: "guestinfo.ignition.config.data"
value: "{{ lookup('file', 'ignition-k3s.json') | b64encode }}"
- key: "guestinfo.ignition.config.data.encoding"
value: "base64"For production scenarios, a 3-node cluster with embedded etcd is recommended:
--cluster-init--server https://<VIP>:6443 --token <token>Load balancer (VIP) can be provided via kube-vip or keepalived.
This creates highly available control planes that can be provisioned in minutes – ideal for tenant clusters or staging systems.
In industries with high compliance requirements, details matter:
A particularly strong use case: end-to-end tests per pull request.
This is reproducible, parallelizable, and without a shared cluster – perfect for fail fast, fix fast.
In comparison, Ansible+Flatcar+vSphere offers advantages especially in traditional data centers and regulated industries, as it integrates seamlessly into existing VMware ecosystems – without an additional platform layer.
With Ansible, Flatcar, and k3s on vSphere, Kubernetes control planes can be provided in regulated environments standardized, securely, and reproducibly.
The result:
Anyone operating Kubernetes in industry or regulated sectors today needs exactly this: automation with clear governance – not click-ops.
In traditional infrastructures, monitoring was a manual process: a new server was rented, an …
Operating a modern IT infrastructure today often feels like being a mechanic who needs a different …
What Operators Face Now – and Which Alternatives Are Truly Viable MinIO has put its Community …